At one time we had to think of Internet connectivity only from the perspective of desktop and laptop computers. Then it went on to personal digital assistants (PDAs) and other handhelds, followed by mobile phones, industrial instruments and machinery. Now it’s even existent in printers, televisions and cars, and the future sees it in cameras, microwaves and washing machines too!
What is the best possible way to make Internet-capable embedded systems for these innumerable devices? Do we need special processors? What kind of operating systems? How do you make the systems smaller, cooler and faster? How can we make them interoperable and secure? Which are the best interfaces and protocols?
As more and more people try to find the best answers to these questions, pledging their knowledge and skills to the realisation of the ‘Internet of Things’—a vision of connecting ambient objects and devices to monitor and control our environment, we see lots of brainwaves and lots of quizzical looks too. Of course, with so many developments around the world it could sometimes get difficult to keep track o where we are heading. In this article, we plan to ease some of those creased brows with an express overview of recent trends concerning embedded Internet systems.
Inside all things, small and big
“The area of networked embedded applications, termed as ‘deeply embedded systems,’ deals with embedded devices connected over a network. It has a multitude of sub areas such as home automation, industrial networks, vehicular automation and wireless sensor networks,” begins Prof. K.R. Anupama, associate professor & head of the department-electrical & electronics engineering, electronics & instrumentation engineering, BITS, Pilani, K.K. Birla Goa Campus. Intel terms this as the fourth phase in the evolution of the Internet; the first being the connection of mainframes, the second being e-commerce and e-mail revolution, and the third being social networking. With embedded systems getting more advanced and so many devices waiting to be connected to the Internet, there is no end to the possibilities.
“Saying that a BMW M5 would support Facebook and Twitter integration is an indication that we are getting there,” quips Sridharan Mani, director and CEO, American Megatrends India. M2M World News Insight says that in 2010 around 22 million connected consumer devices were shipped with the number likely to double in 2011. Forecasts indicate that by 2015 around 270 million consumer devices with embedded connectivity would be shipped.

If you set aside typical computers and look at the embedded Internet market today, it is very evident that mobile telephony is the apple of the industry’s eye. “Embedded devices catering to the mobile segment, like iPhones or Android phones, are most equipped today owing to the widespread adoption of 3G, 4G LTE and other high-speed data networks. With the advent of latest tablet PCs and e-book readers with Internet connectivity using 3G modems, or with Wi-Fi, the mobile telephony segment has the most widespread embedded capability today. This trend is most likely to increase in the future with mobile Internet overtaking desktop Internet, just like how mobiles now outnumber landlines,” explains Mani.
Other consumer electronic (CE) devices such as televisions are also beginning to get connected. Even the averagely-priced models of modern televisions have an ethernet port to access content from the Internet. Similarly, brands like Canon and Samsung also have digital cameras that can connect to the Internet using a Wi-Fi connection, and directly upload pictures to popular photo-sharing websites. There are also video cameras that can stream movies live over the Internet. These are still a preserve of the elite though.
Anup Sable, senior vice president-automotive and engineering, KPIT Cummins feels that household CE devices like kitchenettes, washing machines and ovens will also have connectivity as a key feature in the near future.
Why would you want to have an oven or washing machine that connects to the Internet? Imagine the convenience of being able to ‘connect’ to your oven and set it to start cooking just before you leave from office.Hot dinner ready in a jiffy! If something goes wrong with your washing machine the service person would be able to ‘connect’ to it from his office, diagnose the problem, and perhaps even set it right from there; or at least come equipped with the parts needed to fix the problem during his first visit itself.
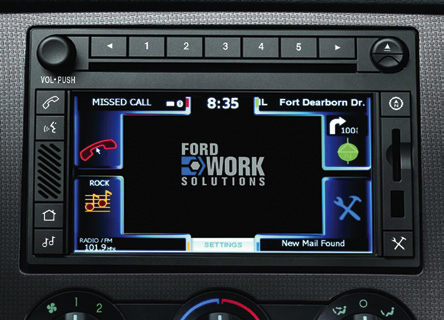
Cars are also getting more Internet-savvy. Although automobiles have long been able to connect to networks—mainly GPS applications—more generalised Internet capabilities are also being talked about now. A number of Internet radios and in-car modems are being introduced in the market; and the latest BMW supports an iPhone application for Facebook and Twitter integration.