Read Part 3
IPv6 can be compared with IPv4 in terms of two important parameters, namely, address space and IP header simplification. A few people projected the death of the Internet due to increased traffic, yet with IPv6, Internet access is guaranteed, with exponential increase in Internet users over time with the provision of abundant address space.

Let us begin with a simple question: Why go for IP version 6 (IPv6), when IPv4 is already standardised and is widely used across the globe? The answer is: IPv4 is crippled with challenges. First, it has 32-bit address scheme. Due to an exponential growth of Internet users, literally the address space of IPv4 is running out of addresses. The exponential growth rate of Internet users in the world just in the last five years is given below, as per the statistics of Internet World Statistics (IWS)/International Telecommunication Union (ITU):
- In December 2013, total users = 2802 million, percentage of world population = 39
- In December 2014, total users = 3079 million, percentage of world population = 42.4
- In December 2015, total users = 3366 million, percentage of world population = 46.4
- In December 2016, total users = 3696 million, percentage of world population = 49.5
- In December 2017, total users = 4156 million, percentage of world population = 54.4
In IP next generation (IPng) or IP version 6 (IPv6), 128-bit address space (in place of 32 bits of IPv4) and minimum 40-byte IP header (in place of minimum of 20 bytes of IPv4) have been proposed. IPv6 is for coping with increasing demands of Internet access. IP addressing for IPv6 is with 128 bits or 16 bytes.
Second, due to the huge growth of Internet users, organisations are being assigned C addresses in IPv4. This is causing an exploration in the routing table of the Internet.
Third, IPv4 is for best effort delivery of packet. It neither guarantees packet sequence integrity nor bonded latency in delivery and is, hence, not suitable for real-time services, like voice and video. Thus, with IPv4, quality voice, video and multimedia services are not being serviced.
On the other hand, growth in voice IP traffic is increasingly huge. IPv6 has been proposed to address the stated limitations of IPv4. IPv6 does so with added features, as given below.
- 128-bit address size ensures address space of about 2128 compared to theoretical maximum of only 232 in IPv4. IPv6 is believed to support trillions of networks.
- Provision for a single address associated with multiple interfaces.
- Auto-configuration facility.
- Provision for quality of service (QoS) support to real-time services like voice and video, and support to mobility.
- Flow level and priority in the header of IPv6 facilitates support of real-time data.
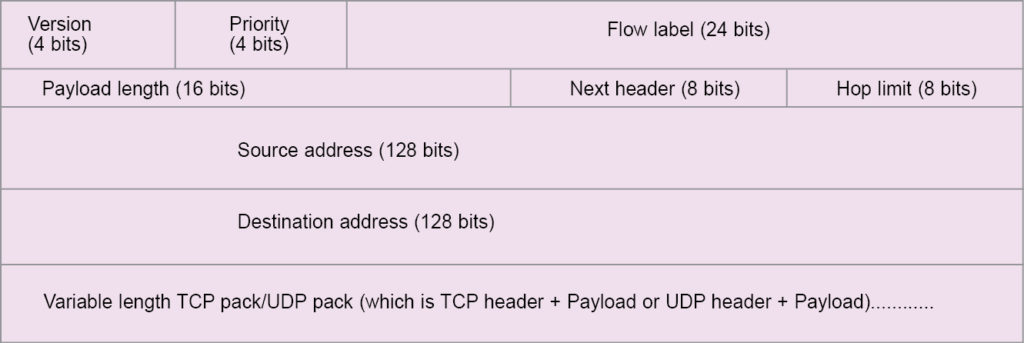
- Efficient header format (Fig. 1) having lesser overhead bits compared to IPv4.
- Fixed header format; header of IPv6 is different from that of IPv4 in many aspects, as follows:
(a) IPv6 has a fixed header size unlike IPv4. Options and padding are variable fields in IPv4. These have been removed in IPv6. This makes IPv6 act in asynchronous transfer mode (ATM) cell in comparison to IPv4, which is a conventional packet in data network.
(b) There is no header checksum in IPv6. This modification is made based on the experience that there is no need for checksum at each intermediate node.
(c) There is no hop-by-hop segmentation procedure in IPv6. Therefore there is no fragment offset, flags and identification fields in IPv6. There is also no need for header length field.
(d) Type of service (TOS) field of IPv4 is removed in IPv6. This removal is also based on experience, as TOS field is hardly used in IPv4.
- IPv6 defines six extension headers: hop-by-hop options, routing, fragment, encrypted security payload, authentication and destination options.
- IPv6 has different options, security and easy transition facility.
Technically, IPv6 can be compared with IPv4 in terms of two important parameters, namely, address space and IP header simplification. A few people projected the death of the Internet due to increased traffic, yet with IPv6, Internet access is guaranteed, with exponential increase in Internet users over time with the provision of abundant address space of 2128.
With a simplified header description, IPv6 is prone to provide multimedia (voice, video and data) services. It is therefore the future replacement of IPv4.
It was felt that a new version after IPv4 should take care of more addresses, reduced overhead, better routing, support for address renumbering, improved header processing, reasonable security, and support for multimedia and mobility. IPv6 has two new fields: flow label and priority. These are included to facilitate the handling of real-time services like voice, video and quality multimedia services.
About IPv6
Salient features of IPv6, also shown in Fig. 1, may be summarised as:
- IPv6 has fixed header bytes like that in an ATM cell, which is of fixed 53 bytes. What is the advantage of having a fixed size? Let us consider the postal system. If envelopes are of variable sizes and weights, processing gets delayed, as the process includes measuring weight, verifying postal stamps required according to weight and so on. If there were fixed-sized and weighted envelopes, postal processing would take much less time and effort. Similarly, with a fixed header, node processing delay is reduced. This makes IPv6 more suitable for real-time services like voice, video and multimedia.
- A 128-bit address space in IPv6, instead of a 32-bit address space in IPv4, is believed to ensure that there will be no exhaustion of Internet address space. It is expected that the Internet under IPv6 supports 1015 (quadrillion) hosts and 1012 (trillion) networks. The Internet under IPv4 can support maximum 232 hosts. IPv6 address space is about 296 times more than that of IPv4. This is how it can ensure that exhaustion of address space is almost unlikely with IPv6.
- Besides unicast and multicast, IPv6 has the provision for anycast addressing that allows a packet addressed to an anycast address to be delivered to any one of the group of hosts.
- IPv6 has the provision for a single address being associated with multiple interfaces.
- Address auto configuration and classless inter-domain routing (CIDR) addressing are provided in IPv6.
- Provision of extension header in IPv6 meets the requirements of such things as checksum, security options, etc.
- Flow-level and priority headers are used to support real-time services. By assigning higher priority to real-time packets, necessity of time sensitiveness is restored. Data packets and, for that purpose, time-insensitive packets are assigned low priority and serviced by the best effort approach.
- IPv6 ensures support for real-time services.
- IPv6 provides security support that could eventually be seen as its biggest advantage. Today, billion-dollar businesses are carried out over the Internet. To keep businesses secure, a public crypto system has emerged as one of the most important tools. IPv6 with its ancillary security protocol has provided a better communication tool for transacting business activities over the Internet.
- IPv6 has the provision for enhanced routing capability, including support for mobile hosts.
Functions of IPv6 headers bytes are given below.
- Version field (4 bits) contains the version number of Internet Protocol. As of now, there are only two versions: 4 and 6. For version 6, this field is six, which makes four bits of this field as 0110.
- Priority (4 bits) field is used to indicate the priority of the datagram. Four bits in the field define 24(=16) priority levels. The first eight priority levels (from 0000 to 0111) are assigned for the services requiring congestion control. If congestion occurs, traffic is backed off.
These are suitable for conventional data and non-real-time services. Different priority levels under the first eight levels are used as 0 for no priority, 1 for background traffic like net-news, 2 for unattended transfer like e-mails, 3 remains reserved, 4 for attended bulk transfer like File Transfer Protocol (FTP), 5 remains reserved, 6 for interactive traffic such as Telnet, X-windows and so on, and 7 for control traffic such as Simple Network Management Protocol (SNMP) and routing protocols.
Higher priority levels (from eight to fifteen) are used for services that do not back off in response to congestion such as real-time traffic. Priority levels eight and fifteen are, respectively, for traffic that is most willing to be discarded on congestion and for traffic that is least willing to be discarded on congestion.
- Flow level (24 bits) is used to identify different data flow characteristics, which may be assigned by the source and can be used to label packets. Packet labels may be required to provide special handling of packets by IPv6 routers. One example of flow-level character is QoS or real-time services. The combination of sender IP address and flow label creates a unique path identifier that is used to route datagrams more efficiently.
Each flow is uniquely defined by the combination of the source address and a non-zero flow label. Flow label can be from 000001h to FFFFFFh in hex. Packets having no flow label are given a zero label. All packets in the same flow must have the same flow label, same source and destination addresses, and same priority level. The initial flow label is obtained by the source using a pseudo random generator, and subsequent flow numbers are obtained sequentially.
- Payload length (16 bits) field indicates the total size of the payload in bytes of the IP datagram that excludes header fields.
- Next header (8 bits) field indicates the header that follows the IP header. The next header can either be one of the optional extension headers used by IP or the header for an upper layer protocols such as UDP or TCP. The field defines the type of extension header. For example, 0, 1, 6, 44, 51 and 80, respectively are for IP, Internet Control Message Protocol (ICMP), TCP, fragmentation header, authentication header and International Standard Organization (ISO).
Each extension header is made of two fields: extension header field and header length field. When there is no need for any other extension header, the next header will be TCP and, hence, it will contain 6. (Here, 6 indicates that there are no more extension headers. And, 6 is written in binary as 0110 in the header.) Length of the base header is fixed at 40 bytes. Extension header gives functional flexibility to IPv6 datagram. Maximum six extension headers can be used.
Extension headers are used for source routing, fragmentation, authentication, security, etc. IPv6 currently defines six extension headers: hop-by-hop option header, routing header, fragment header, authentication header, encrypted security payload header and destination options header. If one or more extension headers are used, these must be in the order as stated above. For example, if destination option, authentication and hop-by-hop option headers are to be used, the extension header fields must be: main IPv6 header, hop-by-hop option header, authentication header, destination option header and then TCP header with data.
Each extension header is associated with one 8-bit next header field. In fragment header, flags and offset fields are fixed at 16 bits. Thus, except in fragment header, in all other extension headers, the next header field is immediately followed by 8-bit extension header length. Header length indicates the length of current extension header in multiple of 8 bytes.
In the last extension header, the next header field contains the value 59. By specifying the next header field as TCP, last of the extension header can be indicated. This is because IP does not only carry TCP segment, it carries UDP pack, ICMP pack, etc, too. To standardise, the last field with value 59 is recommended.
- Hop limit (8 bits) field is used to limit the maximum number of hops that a datagram is allowed to move in the network before it reaches its destination. If after moving the maximum number of hops, as assigned by this field, the datagram does not reach the destination, it is discarded from the network. The field is used to avoid congestion that may be caused by the datagram by repetitive and recursive movements in the network. Each router reduces the hop limit by one before releasing the datagram to the network. When the hop limit reaches zero, it is deleted by the detecting router. Hop limit of IPv6 is exactly time-to-live (TTL) in IPv4.
- IP address of the original source of the datagram is called source address. IP address of the destination of the datagram is called destination address. Each is of 128 bits. Three main groups of IP addresses in IPv6 are unicast, multicast and anycast.
Unicast address is for a particular host. A unicast packet is identified by its unique single address for a single interface network interface card (NIC) and is transmitted point-to-point.
A multicast address is for all hosts of a particular group to receive the datagram.
The anycast address is to address a number of interfaces on a single multicast address.
Unlike IPv4, IPv6 addresses do not have classes. Address space of IPv6 is sub-divided in various ways based on purpose of use. The notion for writing IPv6 address is each double byte of the 16-byte field is separated by a colon. Bytes are written in hexadecimal symbols.
Thus, one example of the address could be 1234:ABCD:56EF:0079:0000:0000:9876:456C.
The proposed notation has the provision to skip leading zeros so that 0000 can be written as 0, or 0056 can be written as 56. It has also the provision of removing one 0, leaving the colons by the technique of double colon notation.
Address of the example given above therefore may be represented as:
1234:ABCD:56EF:79::9876:456C
The double colon notation is used at the beginning and the end of the address but only once. In transition period IPv4, the address would be converted to IPv6 address by pretending 12 bytes of 0s. Thus, IPv4 address 100.45.28.17 may be expressed as:
::100.45.28.17, as an equivalent IPv6 address.
It is found that several fields of IPv4 are no longer in IPv6. Notably among these are checksum, option and fragmentation fields. One of the primary goals of designing IPv6 was the fast processing of packets. Error check is done at upper layers, namely TCP/UDP in IPv6. With no option field, IPv6 is made of fixed size frame, reducing node processing delay. However, scope of extension of the header exists in IPv6. Scope of fragmentation is made a function of source only in IPv6, unlike at every router in IPv4.
Using extension headers
Hop-by-hop extension header
The payload length field of IPv6 defines the maximum payload size in bytes. Thus, maximum size of the payload is limited to 65,535 bytes. Many applications like those of multimedia services may require payloads in sizes larger than 65,535 bytes. Hop-by-hop extension header supports larger payloads, above 65,535 bytes. This extension header may increase the size of payload by 219 bytes.
Header length of the extension header specifies the data in extension in bytes in multiples of 8 bytes. Therefore each extension header can accommodate about 28 bytes. The allowed maximum six extension headers limit may increase the size of the payload by six times of 28. Thus, maximum size of payload becomes about 219 bytes.
There is also a provision for construction of jumbo packet formation with 32-bit field of payload header. Once specification of jumbo packet is adopted, payload size can be as large as 4,294,967,295 bytes (maximum).
Routing extension header
It is typically that of loose source and record routing (LSRR) option field of IPv4 and is used to provide addresses of routers that IPv6 packets shall follow to reach the destination node. This is useful for sending packets by the virtual circuit switching mode of store and forward technique. This makes IPv6 support time-sensitive services of large data.
Fragment extension header
It is used for the purpose of fragmentation of packets as in IPv4. Minimum IPv6 packet size is 1280 bytes. When the receiving node is on a network that has maximum transfer unit (MTU) and is less than 1280 bytes, the sender fragments the packets. By fragmentation, packets are made of the size that the network may carry.
Details of fragmentation are conveyed to the receiving node by fragment extension header. For example, when the packet is fragmented, each part of that packet is assigned the same identification number. Identification number is of 32 bits and the same is notified in variable extension header field. In IPv4, intermediate nodes may fragment data. In IPv6, only original sender or node can fragment data.
Authentication extension header
This is used to authenticate that the original packet sent by the sender is received perfectly by the receiver. When extension header is included, variable extension header fields will include the authenticated code like that of MD5 (message Digest 5) or digest by hash function of all headers. Note that the hop count field will change at each hop. Thus, digest is either excluded from the hop count field or its code is made 0 in authentication.
Encapsulating security payload (ESP) extension header
This is used to provide data security to the payload only by means of encryption/decryption technique, ES (Data Encryption Standard). When this header is included, the sender provides security information in variable extension header fields. The receiver using the information in variable extension header fields decrypts the payload.
Internet Control Message Protocol
IPv6 has dropped the fragmentation and reassembly feature at intermediate routers. Data, if required, is fragmented for packetisation at the source only. Reassembling is done at destination only. When an IPv6 packet received by any intermediate router is too large to be carried forward on the outgoing link, the router simply drops the packet and then sends an ICMP error message to the sender. Error message so sent reads like Packet Too Big. The sender on receiving the ICMP error message Packet Too Big fragments the packet in a smaller size and then transmits fragmented packets, each as one unit.
ICMP for IPv4 is used by hosts, nodes, routers and gateways to communicate network layer information to each other. ICMP information is carried as IP payload like TCP or UDP information. ICMP messages are basically used for error reporting, among other tasks. A few examples of ICMP messages are:
- ICMP type 0, code 0 is used to ping with 16-bit identifier and sequence number.
- ICMP type 3, code 0 is used to indicate host unreachable; codes 1, 2, 3, 4 and 5, respectively, indicate the statuses of host unreachable, protocol unreachable, port unreachable, fragmentation required and source route failure, among others.
- ICMP type 4, code 0 is used for congestion control required/destination unreachable status.
- ICMP type 5, code 0 is used for network error; code 1 for host, code 2 for type of service and network, code 3 for type of service and host redirect message, 32-bit gateway address Internet Header, 64-bit original payload.
- ICMP type 8, code 0 is for echo request/reply, 16-bit identifier, 16-bit sequence number, optional data.
- ICMP type 11, code 0 is for time-to-live when expired on transit; code 1 is used when fragmentation reassembly time is exceeded, expiry of TTL, 32 bits unused, Internet header, 64 bits of original payload.
- ICMP type 12, code 0 indicates error parameter problem, 8-bit pointer, rest 24 bits unused, Internet header, 64-bit original payload.
- ICMP type 13, code 0 is used for timestamp request with 16-bit identifier, 16-bit sequence number, 32-bit original timestamp.
- ICMP type 14, code 0 is for timestamp reply with 16-bit identifier, 16-bit sequence number, 32-bit original timestamp, 32-bit receive timestamp, 32-bit transit timestamp.
- ICMP type 15, code 0 is used for information request for address mask with 16-bit identifier, 16-bit sequence number.
- ICMP type 16, code is 0 used for information reply for address mask.
An ICMP message is made of a type field, a code field and the first eight bytes of an IP datagram (Fig. 2). A datagram is for the ICMP message generated in the first place so that the sender knows about the packet that caused the error. An ICMP message is sent as IP datagram with TOS field set to 0 and protocol field set to 1 that defines the ICMP pack.
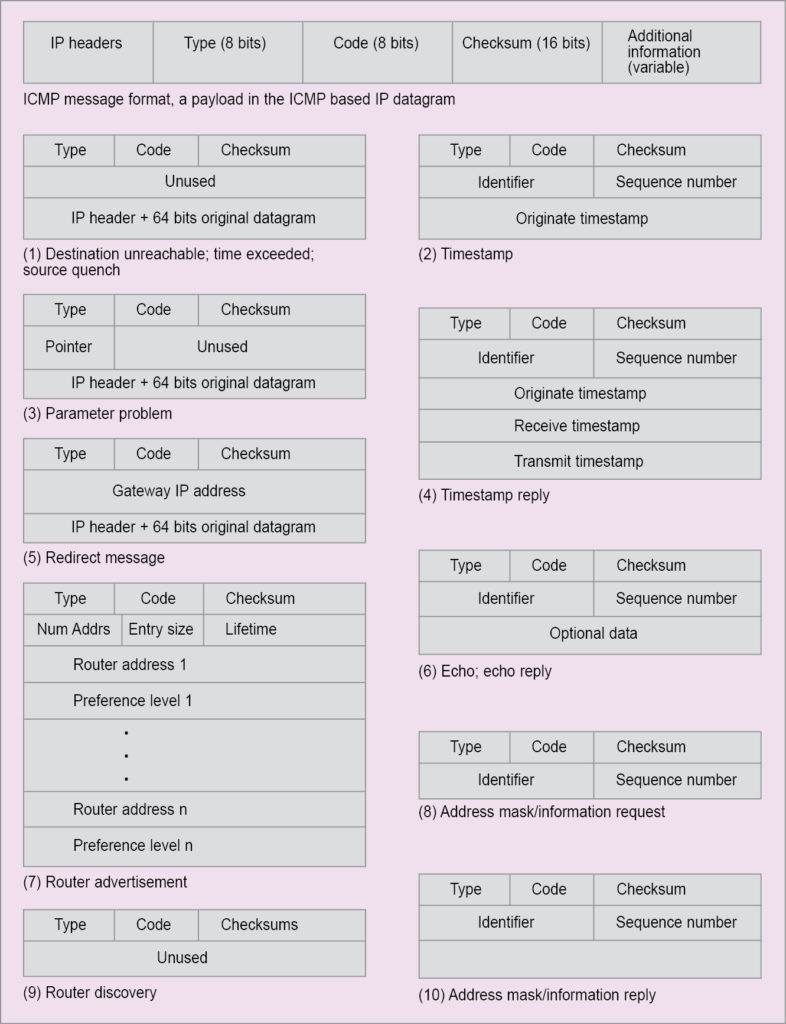
After headers, ICMP message is included as payload. ICMP message format has four parts: 1-byte type field, 1-byte code field, 2-byte checksum field used to provide checksum (1s complement addition) of all 16-bit headers and additional information field, depending on the header of the ICMP message.
For timestamp request, additional information is made of 2-byte identifier, 2-byte sequence number and 4-byte originating timestamp. For echo request and reply, additional information is made of 1-byte identifier, 1-byte sequence number and original IP header. For destination not reachable and others, additional information contains 4 bytes of unused fields, followed by the original IP header.
A new version of ICMP has been defined for IPv6. It does use existing types and codes, but has added new types and codes. Added new ICMP type includes Packet Too Big, Unrecognised IPv6 options and others. Different error-reporting ICMP messages are Destination Unreachable, Source Quench, Time Exceeded, Parameter Problem and Redirect. Various ICMP messages for management query are echo request and reply, timestamp request and reply, address mask request and reply, and router request and advertisement.
This article is dedicated to Internet Engineering Task Force (IETF) for proposing IPv6 to provide global accessibility of the Internet.
Read Part 5
Prof. Chandan Tilak Bhunia is PhD in computer engineering from Jadavpur University. He is also fellow of Institution of Electronics and Telecommunication Engineers, fellow of Institution of Engineers (India) and fellow of Computer Society of India.


